Latest News
News and updates
The latest news from the Yookey world
Data Security in Public Administration: the Key Role of IAM Systems
[INDEX] Authentication tools in Public Administration: MFA and SPID Real-Time Access Control: full audit and traceability…
IAM and Security Incident Management
[INDEX] The role of IAM Systems in Incident Management Why IAM is a key element in…
Privileged Access Management (PAM) and IAM: Security and Access Control
[INDEX] What is PAM (Privileged Access Management) and How It works Difference between IAM and PAM:…
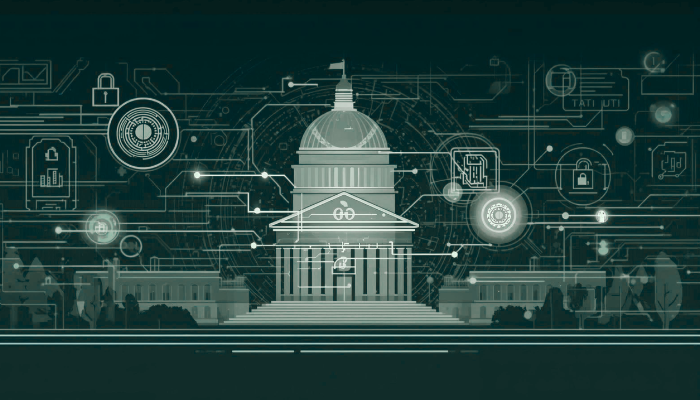
Attribute-Based Access Control (ABAC) and Role-Based Access Control (RBAC) compared
[INDEX] Permission Management: How ABAC and RBAC work Fundamental differences between ABAC and RBAC Policy Maintenance:…
IT Wallet and SPID: updates on digital identity
What is the IT Wallet and what is it for? How does the IT Wallet work…
SPID and CIE: differences and integration with Keycloak
INDEX SPID and CIE compared: how Digital Identities work SPID and CIE Security Levels Enabling SPID…
Role-Based Access Control (RBAC): What is it, benefits and best practices
[INDEX] What is Role-Based Access Control (RBAC)? What are the benefits of implementing RBAC? What does…
IAM systems and gamification: secure training through play
[INDEX] What is gamification and why it enhances e-learning for IAM systems Passwords and MFA: phishing…
IAM and Identity Lifecycle: security from Onboarding to Offboarding
What is identity lifecycle management (ILM)? IAM: why it’s essential for enterprise security Digital Onboarding: how…